Join our Mailing list!
Get all the latest news, exclusive deals, and feature updates.
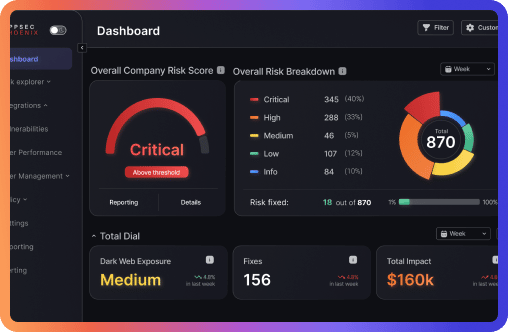
Phoenix Security integrates with your native technology stack, security scanners for Application Security, Infrastructure Security, Cloud Security and Container Security, converting vulnerability into risk.


METASPLOIT
Phoenix security provides weaponization modules that you can use to test your external attack surface and prioritize vulnerabilities accordingly.

Our platform leverages cutting-edge technology to identify recently discovered vulnerabilities before they’re widely exploited. This empowers you to Proactive Security Measures: Patch vulnerabilities quickly and minimize attack surfaces.


Phoenix integrates with Lacework to connect behavioral cloud threat detection with contextual vulnerability remediation. Lacework identifies anomalies across containers and cloud workloads; Phoenix maps those findings to application context, business priority, and developer ownership—enabling focused action across ASPM pipelines.

Phoenix integrates with Sysdig Container to connect runtime detection with application-aware vulnerability management. Sysdig flags container risks in real time; Phoenix maps them to code ownership, business priority, and CI/CD workflows—driving fast, targeted remediation at scale.

Aqua Security and Phoenix Security combine forces to revolutionize cloud-native application security. This integration secures APIs, streamlines CI/CD workflows, and delivers actionable insights, ensuring comprehensive protection from development to production. API Integration and CI/CD integration with Thrivi scanner.

Phoenix and Google Cloud SCC integrate to secure GCP environments from code to cloud. SCC detects risks across cloud assets; Phoenix prioritizes them by business impact and routes actionable tasks to the right teams—reducing noise and accelerating remediation.


Sysdig Cloud surfaces runtime and infrastructure threats. Phoenix transforms those signals into prioritized, code-aware tasks—aligning ASPM with real-time cloud behavior.

Aikido IAS connects identity behavior to code activity. Phoenix turns that visibility into prioritized, automatable risk actions, building identity context directly into ASPM workflows.

Aikido’s AI-powered SAST feeds Phoenix with precision-scored code vulnerabilities, enabling rapid triage, ownership mapping, and automated ASPM workflows without developer drag.

Arnica and Phoenix integrate to merge pipelineless software composition analysis with contextual remediation logic, creating a unified ASPM layer for third-party risk control.

Phoenix integrates with Aikido’s AI-enhanced SCA to deliver focused remediation and intelligent automation across application security posture management workflows.

The Phoenix–Arnica SAST integration fuses real-time static analysis with contextual prioritization, driving focused remediation across CI/CD without developer disruption.

Arnica’s identity-aware access controls connect with Phoenix’s contextual engine to surface exposure tied to overprivileged identities, automating ASPM workflows with actionable precision.

The Phoenix-Orca container integration connects agentless runtime visibility with business-aware vulnerability prioritization, redefining ASPM from image scan to cloud deployment.

Orca Cloud and Phoenix Security integrate to create an ASPM powerhouse—merging agentless discovery with real-time prioritization to secure application infrastructure at every layer.

Phoenix Security integrates with Orca SAST to elevate static analysis with context-aware prioritization. From commit to runtime, teams gain precision in vulnerability management and seamless DevSecOps automation.

Semgrep SCA Phoenix security
Phoenix Security’s integration with Semgrep Supply Chain (SCA) combines reachability-based scanning of open-source dependencies with ASPM-driven prioritization. The scanner identifies which vulnerabilities in third-party code are actually exploitable—so teams fix what matters most, faster.

Phoenix Security and Semgrep SAST come together to streamline vulnerability management by combining pattern-based static analysis with ASPM intelligence. Semgrep scans code for flaws and data flow issues; Phoenix prioritizes what’s actionable based on real risk.

Phoenix Security integrates with Prisma™ Cloud, a cloud-native security platform enabling you to secure your cloud-native infrastructure and applications using a single dashboard.

MEND.IO

Phoenix Security integrates with Mend to help secure developers’ applications, helping them deliver quality, secure code faster. Removing the AppSec burden, we free developers to build secure apps.

Acunetix is an automated web application security testing tool that audits your web applications by checking for vulnerabilities like SQL Injection, Cross-site scripting and other exploitable vulnerabilities.

Phoenix Security integrates with Netsparker. netsparker is a Web application Proof-Based Scanning To Find Real Vulnerabilities in web and API

Automatically share crucial vulnerability data to the relevant Teams channels.

Automatically share crucial vulnerability data to the relevant Slack channels.

Automatically create, assign and track ServiceNow incidents containing the right fix to each vulnerability

Automatically create, assign and track Jira tickets containing the right fix to each vulnerability.

Prioritize and fix vulnerability scan findings across applications deployed on AW.

Ingest Docker container data from AWS ECR to enrich asset risk posture and better prioritize vulnerabilities.

Ingest container data from AWS ECS to enrich asset risk posture and better prioritize vulnerabilities.

Prioritize and fix WhiteHat application security findings across web applications and code projects.

Prioritize and fix pen-testing and bug-bounty findings discovered by HackerOne.

Prioritize and fix pen-testing and bug-bounty findings discovered by Bugcrowd.

FORTIFY
Prioritize and fix Fortify security findings across web applications.

We accept suggestions on integrations from clients and vendors. Please go to www.phoenix.security/integration or www.phoenix.security/contact-us
An asset is a collection of:
The Phoenix Security team can help you calculate assets required with free unlimited asset assessment. By the end of the assessment you’ll know how many assets you require.
Trusted by more than 1000 users and 380 organizations
Learn more about how we can work together.

Derek Fisher – Head of product security at a global fintech. Speaker, instructor, and author in application security.
Derek is an award winning author of a children’s book series in cybersecurity as well as the author of “The Application Security Handbook.” He is a university instructor at Temple University where he teaches software development security to undergraduate and graduate students. He is a speaker on topics in the cybersecurity space and has led teams, large and small, at organizations in the healthcare and financial industries. He has built and matured information security teams as well as implemented organizational information security strategies to reduce the organizations risk.
Derek got his start in the hardware engineering space where he learned about designing circuits and building assemblies for commercial and military applications. He later pursued a computer science degree in order to advance a career in software development. This is where Derek was introduced to cybersecurity and soon caught the bug. He found a mentor to help him grow in cybersecurity and then pursued a graduate degree in the subject.
Since then Derek has worked in the product security space as an architect and leader. He has led teams to deliver more secure software in organizations from multiple industries. His focus has been to raise the security awareness of the engineering organization while maintaining a practice of secure code development, delivery, and operations.
In his role, Jeevan handles a range of tasks, from architecting security solutions to collaborating with Engineering Leadership to address security vulnerabilities at scale and embed security into the fabric of the organization.

Jeevan Singh is the Director of Security Engineering at Rippling, with a background spanning various Engineering and Security leadership roles over the course of his career. He’s dedicated to the integration of security practices into software development, working to create a security-aware culture within organizations and imparting security best practices to the team.
In his role, Jeevan handles a range of tasks, from architecting security solutions to collaborating with Engineering Leadership to address security vulnerabilities at scale and embed security into the fabric of the organization.

James Berthoty has over ten years of experience across product and security domains. He founded Latio Tech to help companies find the right security tools for their needs without vendor bias.


Chris Romeo is a leading voice and thinker in application security, threat modeling, and security champions and the CEO of Devici and General Partner at Kerr Ventures. Chris hosts the award-winning “Application Security Podcast,” “The Security Table,” and “The Threat Modeling Podcast” and is a highly rated industry speaker and trainer, featured at the RSA Conference, the AppSec Village @ DefCon, OWASP Global AppSec, ISC2 Security Congress, InfoSec World and All Day DevOps. Chris founded Security Journey, a security education company, leading to an exit in 2022. Chris was the Chief Security Advocate at Cisco, spreading security knowledge through education and champion programs. Chris has twenty-six years of security experience, holding positions across the gamut, including application security, security engineering, incident response, and various Executive roles. Chris holds the CISSP and CSSLP certifications.

Jim Manico is the founder of Manicode Security, where he trains software developers on secure coding and security engineering. Jim is also the founder of Brakeman Security, Inc. and an investor/advisor for Signal Sciences. He is the author of Iron-Clad Java: Building Secure Web Applications (McGraw-Hill), a frequent speaker on secure software practices, and a member of the JavaOne Rockstar speaker community. Jim is also a volunteer for and former board member of the OWASP foundation.
Get all the latest news, exclusive deals, and feature updates.

