Join our Mailing list!
Get all the latest news, exclusive deals, and feature updates.
Phoenix Security has been selected as one of the leading vendors for the Gartner Hype Cycle for Application Security in ASOC
ASOC tools automate security testing within and across the Software Development Life Cycle, ingesting data from multiple sources. These application security tools correlate and analyze findings to centralize vulnerability management efforts for easier interpretation, triage and remediation. Acting as a management orchestration layer and control, ASOC tools bridge the gap between application development and security testing, ensuring efficient and automated security measures are integrated into the development process. This helps organizations enhance their application security posture and accelerates the identification and resolution of security risks.

Not all security issues and vulnerabilities are equally important. Which vulnerability would you resolve: A vulnerability on asset exposed over the web or an internal system shielded by security controls? Phoenix Security Auto-Prioritization enables you to select which vulnerability is most likely to get exploited.
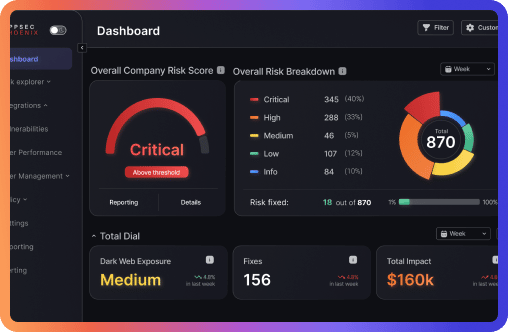
Cyber risk quantification provides a relatable way to measure exposure and risk for the business. Phoenix Security correlates vulnerability results, delivering an AI based auto updating model that correlates application security, Cloud and Container security providing a single risk based pane of glass.
How much are critical applications really worth? How much productivity damage would you lose? Phoenix Security automatically calculates and updates your cybersecurity monetary exposure leveraging FAIR methodologies and AI based Risk modelling.
Because testing tools output large amounts of data, teams tend to spend time and resources aggregating this information into something actionable. Phoenix Security centralizes, analyzes, and correlates security tooling information into a single risk based pane of glass to craft better plans for future development.
Application security, Cloud security, and Container security: how are they correlated? AppSec Phoenix enables you to centralize vulnerability results across different domains. Phoenix Security SMART tags enable automatic and dynamic correlation of application security and Cloud security deployment to always have an updated risk profile of your applications and where they run.
Measure team performance, track resolution time, path to green and how long it takes to resolve vulnerabilities. Provide application security and CISO with predictable and measurable progress.

The Phoenix Security Cloud Platform helps organizations ACT on risk by understanding which vulnerabilities post the greatest risk to individual assets and the potential damage they could cause.
Measure risk, ACT on your vulnerabilities through a single, dynamic pane of glass view on your risk posture.
The Phoenix Security platform provides unparalleled insight into the levels of risk across your business through risk-based graphical models.

The Phoenix Security platform enables you to understand the security posture of your endpoints and the software they are developed on.


For AppSec and DevSecOps teams. Prioritize AppSec vulnerabilities and scale application security programs with risk-based approach

Prioritize Cloud misconfiguration and scale Cloud security programs with risk-based approach

ACT fast on Risk and fix the vulnerabilities and misconfigurations that matter most. Drive risk-based actions and set targets for engineers based on risk profile.

For SOC and SecOps teams. Prioritize vulnerability and scale vulnerability management programs with risk-based approach

Know the asset that you own, what’s assessed and act fast on the vulnerabilities that matter most. Asset management and risk assessment all in one.

Phoenix Security empowers security teams to act fast on exploited vulnerabilities and when threat actors exploit them in the wild. Automate Ticket opening, escalation and block vulnerabilities going to production.

Cloud Security Posture Management- correlate application security and Cloud security in one single place, allowing you to control and act on the most important misconfigurations

Application security posture management -automates the identification of software assets as well as the tracking and scheduling of all application security tools and processes

Trusted by more than 1000 users and 380 organizations

Derek Fisher – Head of product security at a global fintech. Speaker, instructor, and author in application security.
Derek is an award winning author of a children’s book series in cybersecurity as well as the author of “The Application Security Handbook.” He is a university instructor at Temple University where he teaches software development security to undergraduate and graduate students. He is a speaker on topics in the cybersecurity space and has led teams, large and small, at organizations in the healthcare and financial industries. He has built and matured information security teams as well as implemented organizational information security strategies to reduce the organizations risk.
Derek got his start in the hardware engineering space where he learned about designing circuits and building assemblies for commercial and military applications. He later pursued a computer science degree in order to advance a career in software development. This is where Derek was introduced to cybersecurity and soon caught the bug. He found a mentor to help him grow in cybersecurity and then pursued a graduate degree in the subject.
Since then Derek has worked in the product security space as an architect and leader. He has led teams to deliver more secure software in organizations from multiple industries. His focus has been to raise the security awareness of the engineering organization while maintaining a practice of secure code development, delivery, and operations.
In his role, Jeevan handles a range of tasks, from architecting security solutions to collaborating with Engineering Leadership to address security vulnerabilities at scale and embed security into the fabric of the organization.

Jeevan Singh is the Director of Security Engineering at Rippling, with a background spanning various Engineering and Security leadership roles over the course of his career. He’s dedicated to the integration of security practices into software development, working to create a security-aware culture within organizations and imparting security best practices to the team.
In his role, Jeevan handles a range of tasks, from architecting security solutions to collaborating with Engineering Leadership to address security vulnerabilities at scale and embed security into the fabric of the organization.

James Berthoty has over ten years of experience across product and security domains. He founded Latio Tech to help companies find the right security tools for their needs without vendor bias.


Chris Romeo is a leading voice and thinker in application security, threat modeling, and security champions and the CEO of Devici and General Partner at Kerr Ventures. Chris hosts the award-winning “Application Security Podcast,” “The Security Table,” and “The Threat Modeling Podcast” and is a highly rated industry speaker and trainer, featured at the RSA Conference, the AppSec Village @ DefCon, OWASP Global AppSec, ISC2 Security Congress, InfoSec World and All Day DevOps. Chris founded Security Journey, a security education company, leading to an exit in 2022. Chris was the Chief Security Advocate at Cisco, spreading security knowledge through education and champion programs. Chris has twenty-six years of security experience, holding positions across the gamut, including application security, security engineering, incident response, and various Executive roles. Chris holds the CISSP and CSSLP certifications.

Jim Manico is the founder of Manicode Security, where he trains software developers on secure coding and security engineering. Jim is also the founder of Brakeman Security, Inc. and an investor/advisor for Signal Sciences. He is the author of Iron-Clad Java: Building Secure Web Applications (McGraw-Hill), a frequent speaker on secure software practices, and a member of the JavaOne Rockstar speaker community. Jim is also a volunteer for and former board member of the OWASP foundation.
Get all the latest news, exclusive deals, and feature updates.
